Spring4Shell (CVE-2022-22965) FAQ: Spring Framework Remote Code Execution Vulnerability - Blog | Tenable®

M01 - Part 2 Hands-0n Project 2-1 Exploring Common Vulnerabilities and Exposures (CVE) - 4 This page - StuDocu

IPA Information-technology Promotion Agency, Japan : IPA/ISEC:Vulnerabilities:CVE (Common Vulnerabilities and Exposures) Overview
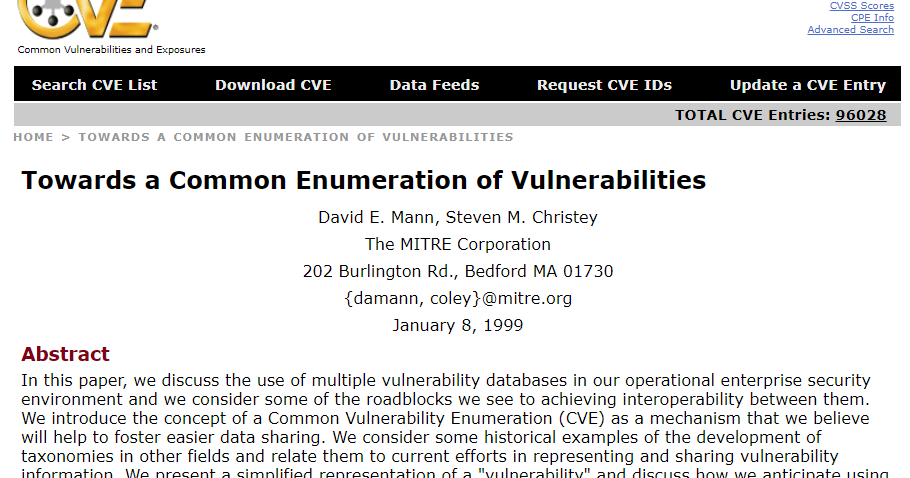
Adventures in Automation: Introduction to Vulns, Common Vulnerabilities and Exposures, the CVE List, and the National Vulnerability Database